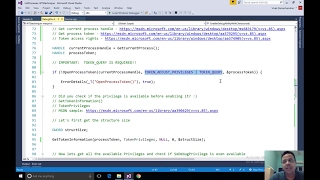
Web Reference: Mar 27, 2024 · In the ever-evolving landscape of cybersecurity threats, attackers continually seek out vulnerabilities within system architectures, often leveraging native Windows Application Programming Interfaces (APIs) to conduct malicious activities. Apr 24, 2025 · This document details techniques for exploiting Windows API functions through Python, focusing primarily on token privileges, process manipulation, and impersonation attacks. Learn and delve into Windows security with a focus on process or thread tokens and the Pass-The-Hash technique, crucial for red teams and penetration testing.
YouTube Excerpt: How does malware leverage the
Information Profile Overview
Windows Api Exploitation Processes Tokens - Latest Information & Updates 2026 Information & Biography

Details: $32M - $48M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 3, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.