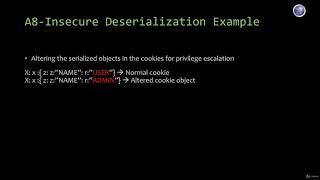
Web Reference: Nov 21, 2024 · Web Application Pentesting learning path > Advanced Server-Side Attacks > Insecure Deserialisation: Get in-depth knowledge of the deserialisation process and how it poses a... Insecure deserialization occurs when untrusted data is used to abuse the logic of an application, inflict a denial of service (DoS) attack, or even execute arbitrary code when data is deserialized. Deserialization, conversely, is the process that counteracts serialization. It involves taking data that has been structured in a specific format and reconstructing it back into an object.
YouTube Excerpt: Social Media ⭐ Discord: https://discord.gg/4hRGHvAhpE Twitter: https://twitter.com/nagasainikhil Github: ...
Information Profile Overview
Webapp Pentesting 18 Insecure Deserialization - Latest Information & Updates 2026 Information & Biography

Details: $43M - $70M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 4, 2026
Information Outlook & Future Earnings
Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.








