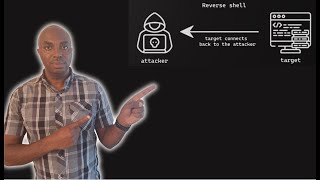
Web Reference: Feb 9, 2024 · When attacking a remote system, a possible goal is to gain initial access by letting the system run arbitrary code. This initial access can then be used to obtain a shell on the target. These... In this lab, we will be using netcat to create a bind shell on a metasploitable machine. If you are unfamiliar with metasploitable, it is an intentionally vulnerable machine which can be loaded in VMware or VirtaulBox, the same as Kali Linux. You can download the metasploitable ISO file here: https://docs.rapid7.com/metasploit/metasploitable-2/ You... Apr 18, 2022 · We have learned about how to use Netcat, what are bind and reverse shells, how to create them using Netcat, and finally, we have broken down the mkfifo netcat one-liner.
YouTube Excerpt: Protect your grandma from RATS: https://bit.ly/bdnetworkchuck (try Bitdefender for FREE for 120 days) Links and Guide: ...
Information Profile Overview
Netcat Bind Shell Hacking Coding - Latest Information & Updates 2026 Information & Biography

Details: $66M - $106M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 6, 2026
Information Outlook & Future Earnings
Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.








