Web Reference: It provides a more complete set of security-specific coding guidelines targeted at the Java programming language. These guidelines are of interest to all Java developers, whether they create trusted end-user applications, implement the internals of a security component, or develop shared Java class libraries that perform common programming tasks. Jul 23, 2025 · However, bugs produced through vulnerable programming practices can have serious security ramifications and could appear in any layer of the stack. In this article, we will list some standard programming practices in Java to protect sensitive data. Jul 24, 2025 · In a time when cyberattacks are increasingly common, securing sensitive data in backend applications is essential. In this article, we’ll explore how to build a simple and secure user...
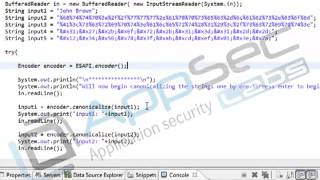
YouTube Excerpt: Java Secure Coding: Data Confidentiality and Integrity 12 3 Hashing
Information Profile Overview
Java Secure Coding Data Confidentiality - Latest Information & Updates 2026 Information & Biography

Details: $8M - $20M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 6, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.