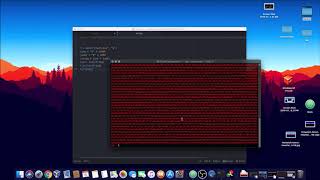
Web Reference: Feb 19, 2019 · Below, we will explore how stack-based overflows work and detail the mitigation strategies that are put in place to try to prevent them. Understanding stack-based overflow attacks involves at least a basic understanding of computer memory. Dec 17, 2024 · It covers common overflow types — stack-based, off-by-one, BSS, and heap — and shows how attackers use techniques like NOP-sledding to gain elevated privileges. Finally, it illustrates how to craft a working exploit by injecting shellcode into a vulnerable application’s memory space. Jan 29, 2025 · Stack-based buffer overflows, which are more common among attackers, exploit applications and programs by using what is known as a stack memory space used to store user input. In the examples, we do not implement any malicious code injection but just to show that the buffer can be overflow.
YouTube Excerpt: Keep on learning with Brilliant at https://brilliant.org/LowLevelLearning. Get started for free, and hurry — the first 200 people get ...
Information Profile Overview
How To Exploit Stack Based - Latest Information & Updates 2026 Information & Biography

Details: $50M - $94M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 6, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.