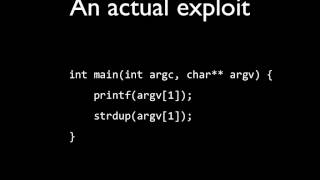
Web Reference: Apr 22, 2018 · I always had hard times to fully understand how to exploit Format Strings vulnerabilities. After a recent online challenge, I decided to tackle this problem and learn how to properly exploit them. The Format String exploit occurs when the submitted data of an inputstring is evaluated as a command by the application. In this way, theattacker could execute code, read the stack, or cause a segmentationfault in the running application, causing new behaviors that couldcompromise the security or the stability of the system. To understand the attac... Sep 15, 2025 · Deep dive into format string vulnerabilities demonstrating how to overwrite the Global Offset Table (GOT) to hijack function calls and spawn shells.
YouTube Excerpt: In this episode we combine the last two videos.
Information Profile Overview
Format String Exploit And Overwrite - Latest Information & Updates 2026 Information & Biography

Details: $48M - $60M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 4, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.