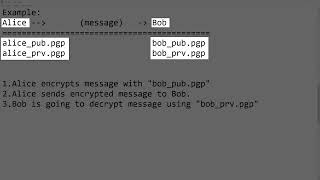
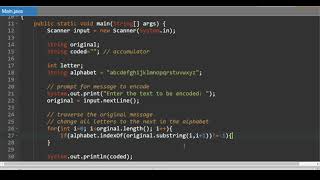
Web Reference: Applications are now able to verify certificates and TLS 1.2 protocol messages using these stronger algorithms and/or sizes. Also, the keytool utility is now able to create and verify keypairs and certificates with these stronger algorithms and key sizes. Dec 11, 2025 · In this article, we learned how to encrypt and decrypt input data like strings, files, objects, and password-based data using the AES algorithm in Java. Additionally, we discussed the AES variations and the size of data after encryption. Jul 15, 2025 · In this article, we will understand the concept in cryptography named symmetric encryption. Before getting into the concept, lets first understand a few key terms involved in cryptography.
YouTube Excerpt: Hi guys we will learn in this tutorial series about the basics of
Information Profile Overview
Cryptography In Java 4 1 - Latest Information & Updates 2026 Information & Biography

Details: $57M - $68M
Salary & Income Sources
Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 4, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.