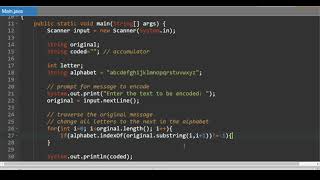
Web Reference: Dec 11, 2025 · In this article, we learned how to encrypt and decrypt input data like strings, files, objects, and password-based data using the AES algorithm in Java. Additionally, we discussed the AES variations and the size of data after encryption. Due to import control restrictions of some countries, the version of the JCE policy files bundled in the Java Runtime Environment 8, 7, and 6 allow strong but limited cryptography. The Java platform strongly emphasizes security, including language safety, cryptography, public key infrastructure, authentication, secure communication, and access control.
YouTube Excerpt: Hi guys we will learn in this tutorial series about the basics of
Information Profile Overview
Cryptography In Java 3 2 - Latest Information & Updates 2026 Information & Biography

Details: $41M - $46M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 4, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.