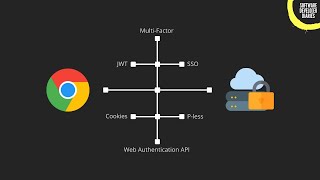
Web Reference: Aug 25, 2025 · A comprehensive guide to choosing the right authentication method for your project. Learn the differences between Basic Auth, Bearer Tokens, OAuth2, JWT, and SSO with practical examples and clear decision criteria for when to use each approach. Authentication is the process that companies use to confirm that only the right people, services, and apps with the right permissions can get organizational resources. It’s an important part of cybersecurity because a bad actor’s number one priority is to gain unauthorized access to systems. Sep 27, 2024 · Authentication is a cornerstone of digital security, serving as the first defense against unauthorized access to sensitive information and systems. This article delves into the concept of authentication, exploring its types, significance, and implementation in today’s digital landscape.
YouTube Excerpt: Become a Senior Software Engineer with a Job Guarantee: ...
Information Profile Overview
Authentication Explained When To Use - Latest Information & Updates 2026 Information & Biography

Details: $47M - $78M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 4, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.