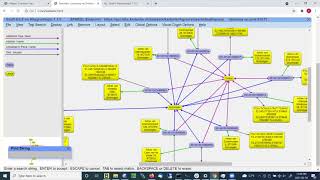
Web Reference: Explore the role of graphs in fortifying cybersecurity defenses. Discover how graph-based analysis unveils hidden threats, patterns, and vulnerabilities, empowering organizations to bolster their security posture against evolving cyber threats. Using our graph visualization and timeline visualization technologies, they’ve been able to build interactive applications that join the dots and reveal the cyber threat intelligence they need to understand. Oct 19, 2024 · Graph theory provides powerful tools for modeling cybersecurity systems, enabling professionals to identify attack patterns, detect anomalies, and enhance overall security.
YouTube Excerpt: Security information and event management/log management (SIEM/LM) evolve continuously to match new security threats.
Information Profile Overview
Applying Graph Visualization To Cyber - Latest Information & Updates 2026 Information & Biography

Details: $10M - $34M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 2, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.